sponsor content What's this?
The Ultimate Checklist for Onboarding a SaaS Vendor
Presented by
Bluescape

Onboarding a new Software as a Service (SaaS) vendor is no small task. While the right vendor can help streamline workflows, improve processes, and maximize efficiencies, evaluating potential partners to ensure they meet your cybersecurity requirements can require a great deal of background research before you ever sign the Statement of Work (SOW).
As an information security leader, you want to be sure that any third-party vendors have a plan to protect your enterprise data, prevent breaches, and remediate vulnerabilities. The following checklist is designed to help you carefully evaluate third-party SaaS vendors to ensure they will make a smart addition to your team.
What to Check for When Choosing a SaaS Vendor:
- Review the vendor’s Software Bill of Materials (SBoM). This should include a thorough listing of all software components, licenses, associated version numbers, and patch statuses.
- Check all open source and third-party codebase components to ensure they won’t introduce any known security vulnerabilities.
- If your company deals in Personally Identifiable Information (PII), ask the vendor how they plan to safeguard it and whether that PII will be shared with any third parties.
- If the answer is yes, who are those third parties and what kind of PII is being shared with them? You should also ask about the third party’s cybersecurity measures.
- Confirm that the vendor is California Consumer Privacy Act (CCPA) and General Data Protection Regulation (GDPR) compliant.
- Determine where your enterprise data will be stored and who will have access to it.
- Will the data travel through overseas servers? If so, where are those servers located and how are they protected?
- Ask how often the vendor scans web servers, applications, and databases for vulnerabilities.
- Ask if the vendor’s threat detection protocols are automated or manual.
- If automated, what processes does the vendor use for automation? Are there any additional security risks associated with those processes?
- Determine if the vendor has any recent complaints, regulatory inquiries, consent decrees, citations, fines, administrative actions, or litigation regarding privacy or data security.
- If so, how long ago was the incident, what was the impact, and what steps has the vendor taken to protect against similar issues moving forward?
- Compare the vendor’s annual audits and security certifications against those of your own security and compliance teams. These should be closely aligned to ensure any potential software partners meet your internal cybersecurity requirements.
- We recommend checking specifically for certifications like ISO 27001 and SOC 2 Type II.
- Conduct a thorough competitive analysis before deciding on a SaaS vendor to understand how they stack up against competitors in the field. Is the vendor transparent and forthcoming about the ways in which they plan to safeguard your data and product?
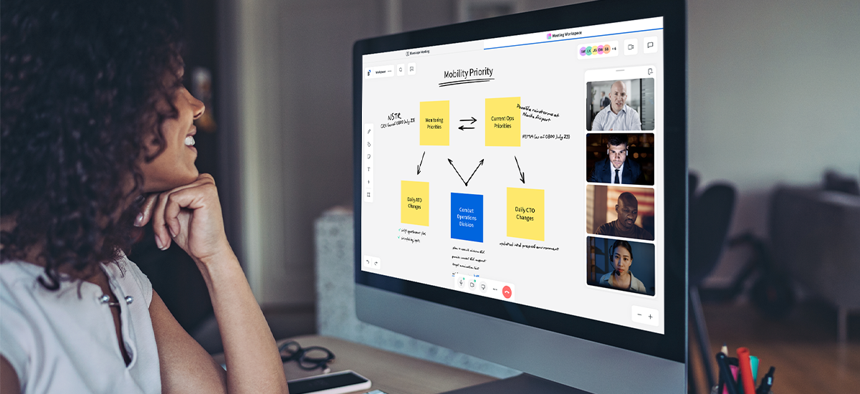
As an information security leader, it’s your responsibility to protect your company from external cyber risks. At Bluescape, we’re committed to empowering virtual collaboration in a way that’s safe, secure, and — most importantly — enjoyable. Give our product a try to see what Bluescape can do for you.
This content is made possible by our sponsor Bluescape; it is not written by and does not necessarily reflect the views of GovExec's editorial staff.
NEXT STORY: Forcepoint Zero Trust CDR Explained






