
Poll Reveals Widespread Unease with Foreign-Based Antivirus Providers
Earlier this year, the US Intelligence Community (IC) released a bombshell report unveiling extensive Russian efforts to undermine public faith in the US democratic process. The influence campaign — a blend of covert cyber espionage, calculated exploitation of social media, and overt messaging by paid Russian ‘trolls’ — placed enormous scrutiny on the vulnerabilities of cyber infrastructure deployed by federal, state, and local governments.
In the ensuing investigation, Russian-owned cybersecurity firm Kaspersky Lab has come under fire for speculation that its popular antivirus service may have enabled Russian intelligence services to steal classified material from the home computer of a National Security Agency (NSA) employee. According to a New York Times report, hackers “turn[ed] the Kaspersky software into a sort of Google search for sensitive information,” effectively granting them a gateway into the code names of American intelligence programs. Even though Kaspersky has denied any and all involvement with the Russian government, the Department of Homeland Security (DHS) issued an operational directive in September mandating federal agencies to identify and remove Kaspersky products from their information systems over the course of 90 days.
To better understand the pervasiveness of Kaspersky products used in the public sector, Government Business Council (GBC) fielded a series of flash polls in October 2017 to federal, state, and local decision-makers. 1,028 employees participated in the survey, 23 percent of whom said they were aware of Kaspersky Lab’s credentials as an antivirus software provider.
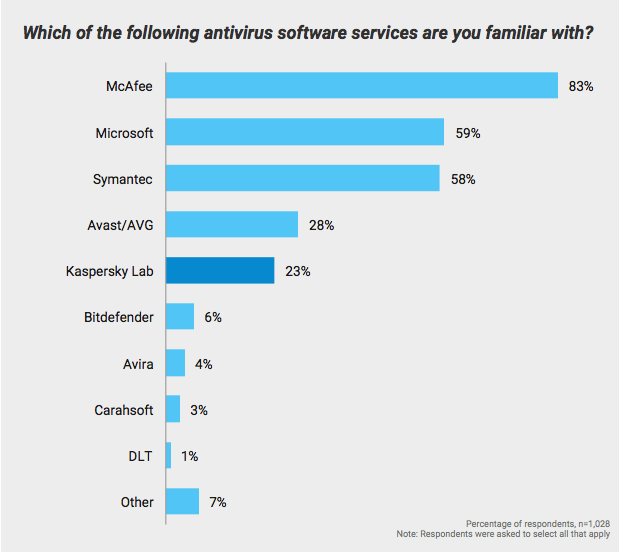
When it comes to brand visibility and awareness, McAfee holds a strong lead over competing antivirus vendors, with 83% of respondents recognizing the company’s foothold in the market. To ensure validity of findings, only those respondents who indicated awareness of Kaspersky Lab as an antivirus provider (23%) were subsequently presented with the following question:
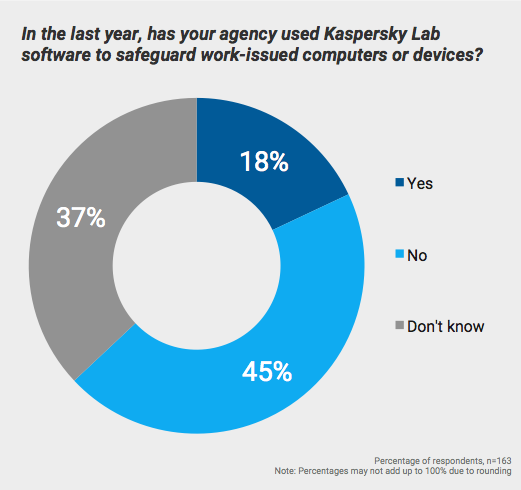
Among those familiar with Kaspersky Lab, close to one-fifth say their agency did use the vendor’s software to safeguard work-issued computers or devices within the last year. 45 percent are reasonably sure that Kaspersky’s products were not employed by their agency, and 37 percent are uncertain if Kaspersky factored into their organization’s cybersecurity at all.
At the moment, federal agencies are still tallying up individual use cases and their plans for eventual removal of Kaspersky software. But according to reporters, known customers include the State Department, Department of Defense, Justice Department, Treasury Department, as well as Army, Navy, and Air Force. And over half of the company’s $633 million in annual sales is traceable to customers in the US and Western Europe, including the agencies listed above.
Given the DHS directive to remove Kaspersky products from government systems, and the intensifying scrutiny of Kaspersky’s potential ties to the Kremlin, GBC wished to investigate government sentiment towards foreign antivirus developers — namely, whether such vendors should be forbidden from government IT. 619 employees representing federal, state, and local levels of government responded to the poll.
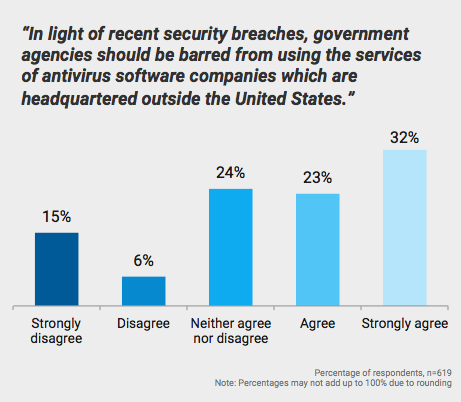
55 percent of employees agree or strongly agree that American government agencies should be barred from using antivirus services of companies with headquarters based outside the US. By comparison, just 21 percent disagree or strongly disagree with that pronouncement, and another quarter of respondents have no opinion on the matter.
Given that a majority of respondents favor restriction of foreign-based software on government IT, it’s clear that improving cybersecurity will remain a major concern going forward, likely to the detriment of companies like Kaspersky Lab. On the same day DHS issued its directive, the Senate also amended the National Defense Authorization Act to include a ban on Kaspersky products.
“Antivirus is the ultimate back door,” says Blake Darché, a former analyst in the National Security Agency (NSA). “It provides consistent, reliable, and remote access that can be used for any purpose, from launching a destructive attack to conducting espionage on thousands or even millions of users.” For that reason, intelligence directors at the CIA, FBI, DIA, and NGA have all said under Senate testimony that they would not be comfortable using Kaspersky products.
In spite of that unparalleled access, the DHS directive does not apply to Kaspersky Threat Intelligence or Kaspersky Security Training products, two other programs that grant the company the same level of access into government systems as their antivirus offerings. It also does not apply to Kaspersky code that is “embedded in the products of other companies,” raising more questions about regulatory extent and the ultimate impact such a ban will have on government cybersecurity.
With Russia’s disinformation campaign and cyber meddling still fresh on the minds of many public servants, a majority of employees are skeptical of granting such unbridled information access to companies based in adversarial nation-states. As the 90-day deadline looms for agencies to remove Kaspersky products from their computers, it’s worth asking whether such actions are sufficient or an omen of greater threats to come.
This post is written by Government Business Council; it is not written by and does not necessarily reflect the views of Government Executive Media Group's editorial staff. For more information, see our advertising guidelines.

