
Image via Kjetil Kolbjornsrud/Shutterstock.com
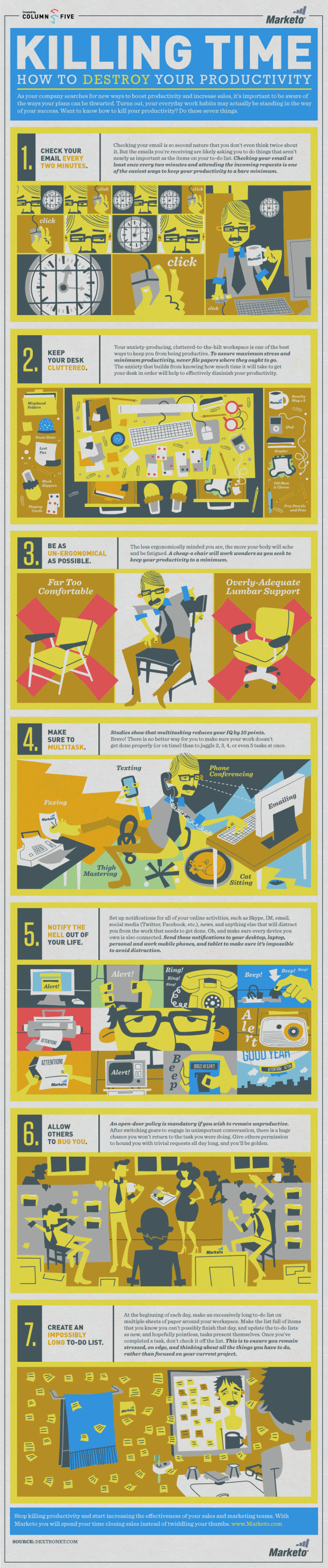
7 Guaranteed Ways to Destroy Your Productivity
Sometimes it's best to explore what not to do...
According to a report from CEB , fiscal austerity has prompted public sector executives to believe they'll need an 18 percent increase in employee performance to meet agency objectives. With some 80 percent of workers indicating their workloads are on the rise, and 59 percent of government agencies anticipating fewer resources, realizing performance gains will be difficult, to say the least.
How can we increase productivity in government? We'll be exploring this very topic at Excellence in Government on May 13 - 14 in Washington, D.C. Sessions will include how to leverage data for better decision making, using technology to increase collaboration and how mission-motivated teams get better results. But, to start, sometimes it helps to define how NOT to do something.
Below we present seven sure-fire ways to destroy your productivity. Pro tips include:
- Incessantly checking your email!
- Multitasking!
- Creating even more calendar/mobile notifications!
- And making really long to-do lists!
Any of these sound like you? Share your productivity killing habits (and perhaps a few solutions) in the comments.
Find more
great infographics
on NerdGraph Infographics
Image via Kjetil Kolbjornsrud/Shutterstock.com







