Author Archive
Aliya Sternstein
Senior Correspondent
Aliya Sternstein reports on cybersecurity and homeland security systems. She’s covered technology for more than a decade at such publications as National Journal's Technology Daily, Federal Computer Week and Forbes. Before joining Government Executive, Sternstein covered agriculture and derivatives trading for Congressional Quarterly. She’s been a guest commentator on C-SPAN, MSNBC, WAMU and Federal News Radio. Sternstein is a graduate of the University of Pennsylvania.
Aliya Sternstein reports on cybersecurity and homeland security systems. She’s covered technology for more than a decade at such publications as National Journal's Technology Daily, Federal Computer Week and Forbes. Before joining Government Executive, Sternstein covered agriculture and derivatives trading for Congressional Quarterly. She’s been a guest commentator on C-SPAN, MSNBC, WAMU and Federal News Radio. Sternstein is a graduate of the University of Pennsylvania.
Features
"Every American Has the Right to Know"
President Obama’s push for transparency into government spending may have run out of steam.
- Aliya Sternstein
Management
The Top 10 Women Cyber Guardians You Should Know About
A roundup of influential information security leaders to watch.
- Aliya Sternstein
Analysis
How the OPM Hackers Killed the Password
The theft of feds’ personal information, not Hollywood’s selfies, might have finally sped up security measures.
- Aliya Sternstein
Analysis
Mapping Threats
New software is helping intelligence analysts, but the most powerful processor is still the human brain.
- Aliya Sternstein
Briefing
Privacy Negotiator
Civil liberties advocate Ari Schwartz walks a fine line between tracking and protecting citizens as White House cyber director.
- Aliya Sternstein
Briefing
Around Government
Braving bureaucracy, malware magnets, building brain hacks.
- Charles S. Clark, Aliya Sternstein and Patrick Tucker
Advice And Comment
The Snowden Effect
Public aversion to domestic spying doesn’t seem to be hurting government’s ability to recruit cyber staff.
- Aliya Sternstein
Thinking Ahead
Cyber Medic
Kevin Charest turned HealthCare.gov’s security challenges into a quest for better teamwork at HHS.
- Aliya Sternstein
Nextgov
Cyber Arms Control
Congress wants agencies to stop the proliferation of war worms, but lawmakers haven’t yet defined what those are.
- Aliya Sternstein
Thinking Ahead
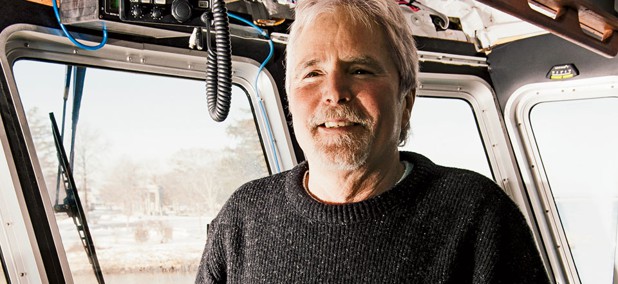
The Whale Whisperer
Biologist David Wiley ventures outside the swim lanes to design an app that prevents deadly ship strikes.
- Aliya Sternstein
Management
Can You Save the Whales With a Smartphone?
NOAA's Whale Alert mobile app can keep mariners from striking the endangered North Atlantic right whale.
- Aliya Sternstein and Ross Gianfortune
Nextgov
Tech Roundup
Apps that teach, the cyber training slide, CMS’ testing troubles.
- Joseph Marks, Aliya Sternstein and Bob Brewin
Briefing
Sensory Overload
DHS and Congress rethink surveillance gear along the U.S.-Mexico border.
- Aliya Sternstein
Nextgov
Tech Roundup
Ghost viruses, ID iris scans, lagging IT reform.
- Aliya Sternstein, Bob Brewin and Joseph Marks
Features
Beyond the Breach
The Thrift Savings Plan bounces back from the theft of personal data on thousands of beneficiaries.
- Aliya Sternstein
Features
NSA's Big Dig
It’s no secret that Harvey Davis has a sensitive job building massive spy data centers.
- Aliya Sternstein
Nextgov
Tech Roundup
Boosting access to federal data, securing mobile devices, the joint health record mess.
- Aliya Sternstein, Bob Brewin and Joseph Marks
Nextgov
Access Denied
DHS is caught up in a decade-long struggle to secure port facilities with biometrics.
- Aliya Sternstein