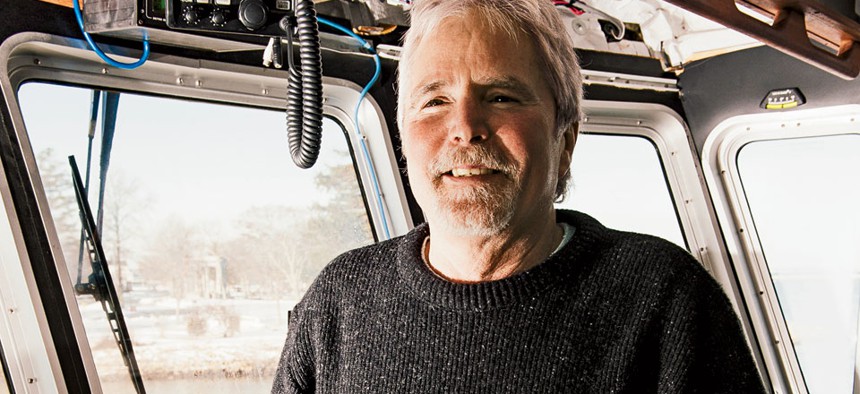
Mark Fleming
The Whale Whisperer
Biologist David Wiley ventures outside the swim lanes to design an app that prevents deadly ship strikes.
David Wiley, a biologist at the National Oceanic and Atmospheric Administration, spearheaded development of an app that pinpoints, on digital nautical charts, places where ships might collide with endangered North Atlantic right whales. Only 500 of the mammals remain. Their biggest threat is boats.
To protect the species, NOAA restricts speed limits and boundaries. Those barriers, however, are invisible in the ocean unless mariners have access to dynamic maps. With NOAA’s Whale Alert app mariners can simply swipe an iPad or iPhone screen to see the no-go zones.
“It’s designed to make it easier for the maritime community to comply with the ship-strike rule,” Wiley says. “Obviously, the more compliance, the more likely we are to have a conservation benefit.”
As of Dec. 6, there had been no fatal collisions in the regions charted by the app since its 2012 launch. And with funding from donations, the tool required only a small government investment.
Wiley went through unofficial channels to make all this happen. NOAA never signed off on the app. The field scientist didn’t know about federal Web management rules. But after the fact, no one is likely to deactivate such a life preserver.
For fostering technology that saves lives, money and time, Nextgov honored Wiley with a 2013 Bold Award.
Next up: A universal Ocean Alert app.
“We’re hoping to evolve Whale Alert into Ocean Alert, because there are similar problems everywhere in the ocean,” Wiley says. “For instance, there are some areas where shippers need to burn different fuels because of air pollution regulations, and they need to know where they are relative to those zones as well.”
NEXT STORY: Messages to the Mid-East







