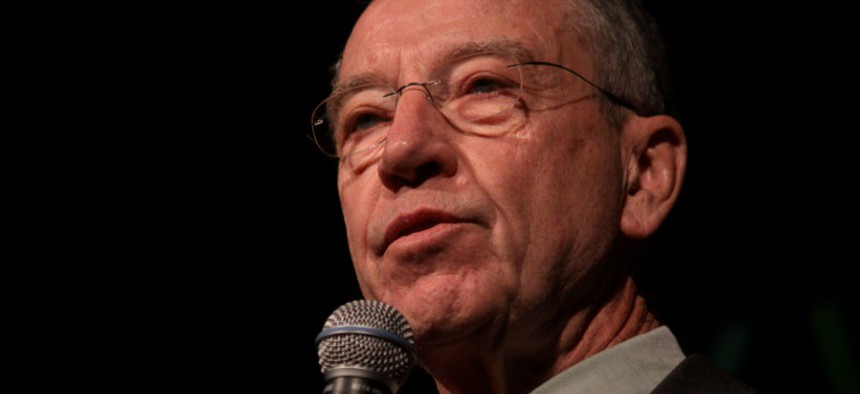
Sen. Chuck Grassley, R-Iowa Flickr user Gage Skidmore
Case of IG Who Sat Idle for 2 Years Continues to Trouble Grassley
Senator asks FBI for more information, says investigation took too long.
The saga of the inspector general who stayed home for two years continues.
Sen. Chuck Grassley, R-Iowa, long critical of the how the government handled a lengthy ethics probe of recently retired National Archives and Records Administration watchdog Paul Brachfeld, is calling in the FBI.
In an Aug. 21 letter to the bureau and the Council of the Inspectors General on Integrity and Efficiency, Grassley complained that the Archives case left that agency without permanent leadership for two years. “Extended investigations are harmful to the independence of the IG community,” he wrote. “They also prevent agencies from effectively resolving allegations against a member of senior leadership.”
Hence, Grassley said, Congress needs data to help it improve the inspector general community’s integrity process. He asked the FBI and the IG council to provide, by Sept. 4, information from 2011 to the present on the following:
- Average and median number of days from receipt of a complaint to an IG until initial referral or closing;
- Average and median number of days for the council’s public integrity committee to review a referral for possible criminal referral;
- Average and median number of days from referral to the integrity committee to when the item appears on the agenda, and so on through the stage at which a report is sent to Congress.
Grassley also asked for FBI data on costs of its probes for the council, the number of full-time employees, and statistics on the number of complaints that result in full investigations.







