
The USS Providence and crew moor at the North Pole. United States Navy
Northern Exposure
The U.S. military charts an eight-point plan for securing the Arctic and its natural resources.
By Kevin Baron
T he Arctic has gained increased attention in national security circles as melting ice caps promise new access to strategic positions and undersea resources for three of the world’s most powerful countries—the United States, Russia and China—as well as Canada and NATO.
Citing American interests in climate change, energy security and the integrity of northern sea lanes, Defense Secretary Chuck Hagel has introduced a new Pentagon plan for Arctic security that promises to significantly increase U.S. military resources and attention to the polar region. The plan is the Defense Department’s follow-on to President Obama’s national Arctic strategy, released in May 2013.
“We are beginning to think about and plan for how our naval fleet and other capabilities and assets will need to adapt to the evolving shifts and requirements in the region,” Hagel told a delegation of international officials last fall.
The United States will not relent in defending Alaska and its northern borders, Hagel said, laying out an eight-point plan:
- Protect U.S. borders and Alaska
- Do more to more study theenvironment
- Enforce the law of the seas
- Evolve Defense Department capabilities and infrastructure
- Increase international training
- Prepare for natural disasters
- Protect the Arctic environment
- Build and enforce international institutions and organizations
A Tangled Web
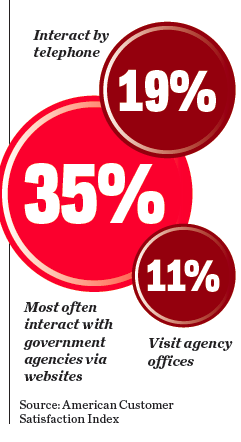
Americans’ satisfaction with federal services declined this year mostly because they find agency websites more difficult to navigate, less reliable and the information less useful, according to a recent American Customer Satisfaction Index report. More than one-third of citizens who interact with government mainly use websites.
Turning the Other Cheek
No agency has embodied the paradoxical cliché across government—doing more with less—during the past few months more than the Office of Personnel Management. In its role of helping agencies with personnel matters, OPM issues furlough guidance, administers hiring freezes and interprets how new laws impact federal pay and benefits.
OPM, however, is not immune from the governmentwide cuts. The agency recently laid off more than 300 employees in its Human Resources Services office. A few days later, OPM sent a memo to all agencies offering its services to help them improve employee morale.
Most agencies could stand some internal improvements. In the 2013 Employee Viewpoint Survey, the percentage of workers giving positive marks decreased in 53 of 55 categories measured.
So OPM finds itself in a difficult position. The future of the federal human resources agency will largely depend on its ability to
help other agencies accomplish their missions with limited resources, while simultaneously managing its own shortfalls.
- Eric Katz
How to spread constructive behavior in your organization.
In their new book, Scaling Up Excellence: Getting to More Without Settling for Less , Robert Sutton and Huggy Rao address the challenges and trade-offs leaders face in spreading constructive beliefs, behaviors and practices in their organizations. The book highlights the strategies behind success stories such as Kaiser Permanente’s patient health records system and Wyeth Pharmaceutical’s model manufacturing processes.
The authors, who are professors of management and organizational behavior, offer a series of lessons for building and uncovering “pockets of excellence” learned through seven years of case study research and conversations with leaders in a variety of industries. They include:
- Spread and sustain a mind-set of excellence, not just a footprint.
- Scaling requires addition and subtraction—the problem of more is also a problem of less.
- Use healthy doses of worry and self-doubt to combat illusion, impatience and incompetence.
- Slow down to scale faster —and better—down the road.
- Learn how to strike a balance between customization and replication.
- Link emotionally hot causes to cool solutions.
- Use hierarchy and process to destroy bad bureaucracy.
- Connect people and cascade excellence, using social bonds to spread the right mind-set.
- Accelerate accountability: Build organizations where “I own the place and the place owns me.”
- Think bad to great, not good to great: Clearing the way for excellence to spread, eliminating destructive beliefs and actions is the first order of business.
- Chawndese Hylton
Tomorrow’s Warhorse
The Defense Advanced Research Projects Agency in 2014 is wrapping up a two-year test of robotic pack mules that can gallop behind military squads in the field and carry up to 400 pounds of equipment. The strain of carrying 100 pounds of gear can severely hamper a warfighter’s readiness, according to the Army and Marines, who have made it a top technology challenge. The Legged Squad Support System, or LS3, is designed to follow visual and verbal commands, and has the ability to traverse rugged terrain and even right itself if it falls.
NEXT STORY: How to Battle Boss Envy






