
Image via Steve Heap/Shutterstock.com
The Secret to Restoring Trust in Government
If trust is a measure of access and influence, social media might be the key.
Yesterday morning, I attended a panel that spoke about a new report released by the communications firm, Edelman, entitled “2013 Edelman Trust Barometer.” The findings, especially those that pertain to US citizens, industries, and institutions, are striking.
Who we trust now
The Trust Barometer examined how various countries’ populations viewed a number of industries, including tech companies, financial service companies, and government as a whole, among others. People had the highest levels of trust in the technology sector, followed closely by the automotive industry. The lowest levels of trust were found in the banking and financial services sectors.
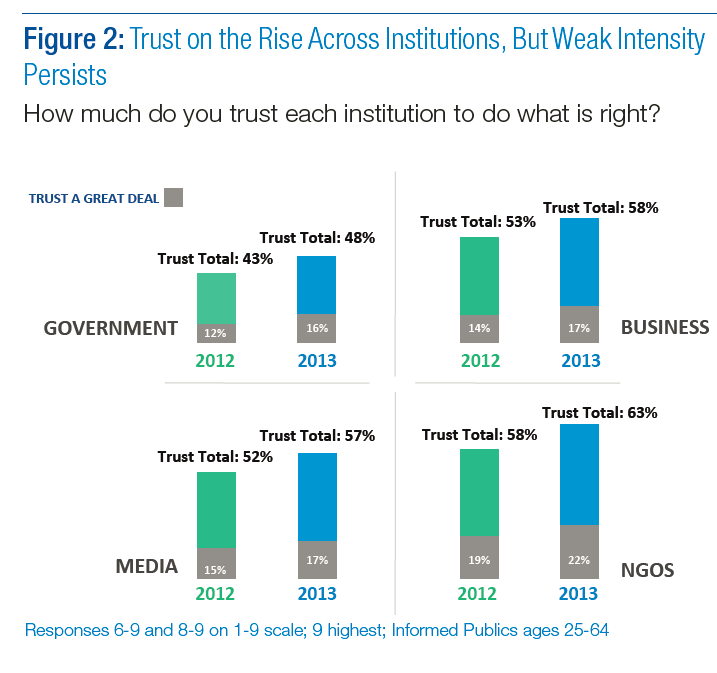
Interestingly—and tellingly—trust in every sector has gone up over the past year, though some more than others. Trust in government, business, the media and nongovernmental organizations (NGOs) has increased by five percent; of those, NGOs enjoy the highest levels of trust.
One important point that I cannot find in the executive summary of the report, but that Edelman’s CEO related in his opening remarks is that what he called “the elite” have a 47 point higher level of trust in the government than everyone else.
Why we trust
It is important to understand why people place their trust in people and institutions, because in doing so, organizations can take steps to earn the trust of their customers, clients, or constituents.
When I look at the data, what strikes me is that people have the greatest level of trust in people and organizations to which they have access and over which they have at least some level of influence. In short, the more people can see what an organization is doing, and how it is doing it, and the more they feel that they have a voice in the organizations goals and activity, the more trust they have in that organization.
Access and influence: open government is a part of this, but only the beginning. People want to know what is happening at all levels of government, but that’s not all. They also want to affect those organizations’ activities, as the Republican House discovered when they launched “America Speaking Out” and the Obama Administration realized when they were overwhelmed by the response to their ePetition site, “We the People.”
What makes the difference
The American people right now have an historically low level of trust right now in their government. Numerous polls have shown very low levels of popularity with Congress, in particular, but individual representatives are fairly popular in their own districts. What makes the difference is that people feel that they have access to and influence over their individual representative, but little access to and no influence over Congress as a whole. And what gives them that access? Social media.
Through social media, citizens can earn the attention of their mayor or governor (for better or worse), and government is expanding the tool-set through which it can engage citizens. As it does, I expect to see levels of trust increase further.
(Images via 2013 Edelman Trust Barometer, Executive Summary)
(Cover image via Steve Heap/Shutterstock.com)







