A Visual History of Presidents Awkwardly Meeting the Losers They Defeated
A photo archive of past presidential contenders giving away exactly how they feel while meeting "the other guy."

Subscribe
:
Newsletter
Facebook
LinkedIn
President Obama and Mitt Romney will have lunch together in the White House Thursday, part of a quadrennial tradition in which we celebrate the peaceful transition of power (or four more years of the same power) and simultaneously watch the former foes' faces for signs of gloating or petulance. The White House says there will be no press coverage of Obama and Romney's meeting, but luckily we have a long photo archive of past presidents' microexpressions giving away exactly how they feel about the other guy. Before we get to this year's afternoon of awkwardness , here's a visual history of the awkward handshakes and fake smiles of post-election meetings past.
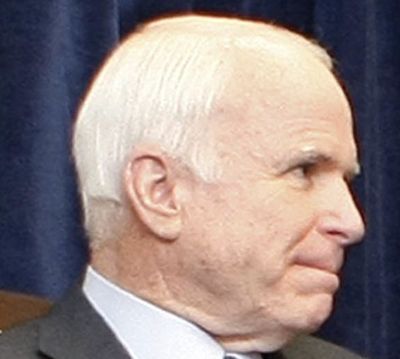
Big bubble of personal space. The distance kept them civil when John McCain and President-elect Obama met November 17, 2008 in Chicago.

But even at that distance, grimaces are hard to hold back.