vectoraart/Shutterstock.com
When Leadership Skills Trump Technical Skills
Subject matter experts promoted to executive posts have to tap a different skill set.
At some point in your career, your leadership skills need to trump your technical skills if you’re going to make the biggest possible impact. Most professionals start their careers as subject matter experts in something. Often, the best subject matter experts get promoted into roles where they’re responsible for leading other subject matter or technical experts.
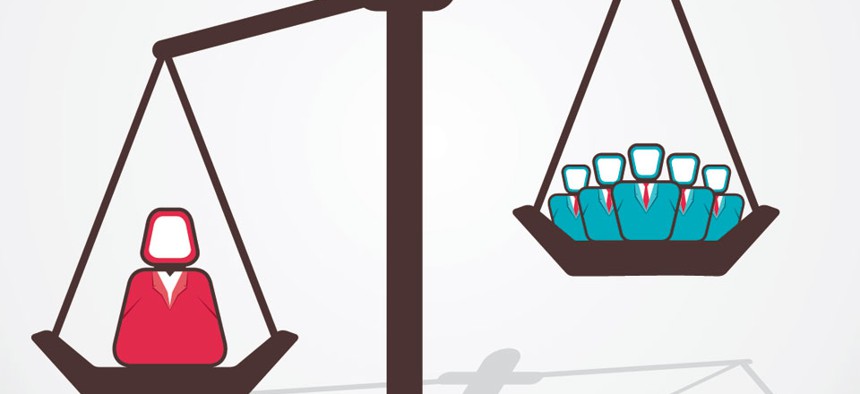
That’s the great inflection point where leadership skills begin to trump technical skills. It’s represented in this simple graph:
As the picture suggests, the higher you rise in leadership, the leverage in getting bigger things done comes from spending less time on your technical skills and more time exercising your leadership skills.
There’s a relatively simple way to prove this out which I’ve used in dozens of Next Level leadership workshops during the past few years. In a roomful of 70 or 80 leaders, I ask everyone to give their answers to this question: What is it, given the leadership role that you’re in, that only you can do?
What follows is, in no particular order, a typical list of answers and some thoughts about what the list tells us:
- Set the vision
- Develop my people
- Get the right people on the team
- Allocate resources
- Establish priorities
- Build the relationships we need to get stuff done
- Provide air cover
- Share perspective and information with the team
- Keep key people informed about what we’re doing
- Knock down barriers
- Keep us focused on the plan
- Monitor and measure progress
When you look at that typical list, what do you notice? Here’s what I notice. There’s not a pure technical skill on the list. It’s all leadership.
What else would you add to the list of things that only the designated leader can do? What are your thoughts on the leadership/technical skills inflection point? What makes it challenging and what can be done to make it easier? Please share your thoughts.
( Image via vectoraart / Shutterstock.com )
NEXT STORY: IRS Reaches Electronic Filing Milestone







