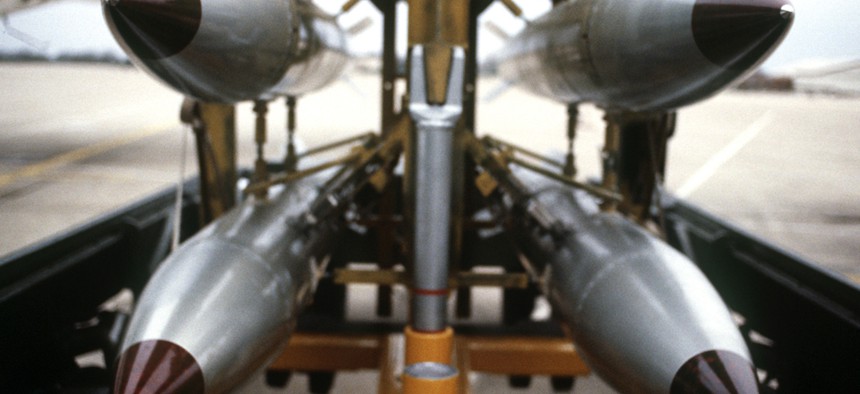
Defense Department file photo
Pentagon: B-61 Bomb Update Faces Possible Delays
Project's time line faces risks from separate work under way at the Defense and Energy departments.
Defense Department experts see a danger of delays in work on a key nuclear-bomb component under development at multiple federal agencies.
Preparation of the new B-61 gravity bomb "tail kit" is currently proceeding on schedule, but the project's time line faces "risks" from separate work under way at the Defense and Energy departments, according to the Pentagon's Systems Engineering office.
"Interdependencies" involving a range of activities at the two departments "present technical challenges and will require close attention and development," the Pentagon office said in a report last month.
The potential coordination hurdles threaten to bog down progress, says the annual assessment for fiscal 2013.
The developmental component for the bomb's tail section is intended to improve the accuracy of the B-61 bomb's forthcoming Mod 12 variant, which is now in its second year of development. The refurbished bomb would eventually stand in for several earlier versions, some of which are fielded at bases in several European countries.
Ultimately, the possible issues may cause the project to miss a goal date for entering full production, as well as a deadline for delivering the first completed tail kit, the document warns. Both goals were scheduled for 2019, the Pentagon said in a Selected Acquisition Report from December 2012.
The authors of last month's analysis added that a "limited number of developmental test flights" could complicate efforts to ensure that the tail kit meets reliability standards. Project managers are already "mitigating 11 risks related to schedule, performance, production, integration and cost," they noted.






