The Federal Government Is Giving Fewer People Security Clearances
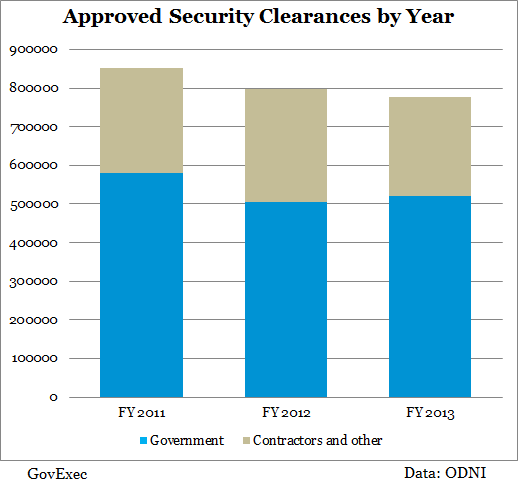
Approved clearances have dipped 9 percent since 2011.
The number of new security clearances provided by the federal government -- both initial clearances and renewals -- has decreased by 9 percent since 2011, according to a new report.
The Office of the Director of National Intelligence released a report showing the number of approved clearances dropped for the second consecutive year in fiscal 2013, to just more than 777,000. While the ODNI attributed the trend to the enforcement of a Clinton administration executive order, one expert said this marked the natural reverse flow after the number of individuals with security clearances had ballooned prior to 2011.
The data are limited – ODNI only started tracking this particular information in 2011, as mandated in the 2010 Intelligence Authorization Act -- but show a clear trend in the last three years.
Intelligence agencies, such as the CIA and National Security Agency, have generally denied security clearance applications at a higher rate than in years past. The NSA, for example, rejected 7.2 percent of security clearance applicants in fiscal 2013, compared to 5.7 percent in fiscal 2012.
ODNI said the report suggested agencies are “reviewing their cleared population…pursuant to Executive Order 12968,” signed by President Clinton in 1995 in an effort to keep the number of employees with “access to classified information to the minimum.” The office did not respond to a request for further explanation as to why a two decade old mandate would suddenly be enforced more strictly.
Nicole Smith, an attorney at the law firm Tully Rinckey who provides representation to employees seeking or denied security clearances, said the reduction was in relation to a period in the mid-2000s when “basically everyone needed a clearance.”
Conducting background investigations “takes time and money,” Smith said. “It is essentially a waste of resources to give individuals clearances who don’t really need [them].” In a time of an extreme budget crunch, especially at the Pentagon, it stands to reason agencies would want to cut back on the number of investigations.
Also, of course, are the security risks inherent in giving too many employees access to classified information. This issue has come to the forefront in recent months, Smith said, with “high-profile cases” such as Edward Snowden and Navy Yard shooter Aaron Alexis. The downward trend predates these cases, however, so any impact they have on the number of security clearances issued will be seen in the months and years ahead.
Smith expects those cases to expedite the trend, as current congressional and Obama administration -led pushes will likely result in more expansive investigations and more “derogatory information” on individuals.
Smith conducted background checks beginning in the early 2000s, and said during her nearly 10 years in the industry there “really weren’t any changes.” Moving forward, when investigators look into “different aspects of someone’s life that isn’t currently being evaluated,” it will inherently lead to fewer approvals.
The ODNI report also showed federal civilians earned more security clearances in 2013 compared to contractors, with government workers’ share of new clearances granted ticking up 4 percentage points. Smith, drawing from her experience representing private-sector workers, speculated investigators are ramping up security clearance denials due to financial considerations and contact with foreign nationals.
( Top image via vistok / Shutterstock.com )







