One Chart Shows One Big Problem With Defense Contracting: Competition Is Declining
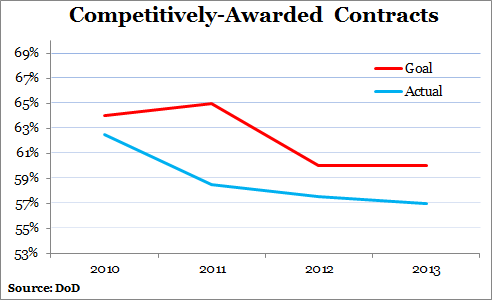
The department in 2010 began setting goals for awarding more work competitively, but it's never been able to hit its targets.
"Competition is the single best way to motivate contractors to provide the best value," according to the Pentagon's latest annual report on the state of the Defense acquisition system, released in June.
Unfortunately, the Defense Department has been losing ground for the last six years in the percentage of contracted work being let competitively each year. In 2008, 64 percent of Defense contract dollars were spent through competitive awards; by 2013, that rate had fallen to 57 percent.
"The erosion is not huge, and I believe that decreasing budgets which limit new competitive opportunities are a major root cause," Frank Kendall, the Pentagon's acquisition chief, told members of the Senate Armed Services Committee in April.
In 2010, the department began setting strategic goals to increase the percentage it spends on competitively-awarded contracts. In September of that year, then-Under Secretary of Defense for Acquisition, Technology and Logistics Ashton Carter issued the memorandum "Better Buying Power: Guidance for Obtaining Greater Efficiency and Productivity in Defense Spending," which, among other things, aimed to lower weapons costs by increasing competition. Building on those goals, Kendall, Carter’s successor, launched the Better Buying Power 2.0 initiative two years later.
Despite those efforts and even lowering the goals over time, the Pentagon has never met them.