Author Archive
Tom Shoop
Former editor in chief, Government Executive
Tom Shoop is the former executive vice president and editor in chief at Government Executive Media Group, where he oversaw editorial operations at Government Executive, Nextgov, Defense One and Route Fifty. He started as associate editor of Government Executive magazine in 1989; launched the company’s flagship website, GovExec.com, in 1996; and served as editor in chief from 2007 to 2021.
Tom Shoop is the former executive vice president and editor in chief at Government Executive Media Group, where he oversaw editorial operations at Government Executive, Nextgov, Defense One and Route Fifty. He started as associate editor of Government Executive magazine in 1989; launched the company’s flagship website, GovExec.com, in 1996; and served as editor in chief from 2007 to 2021.
Management
Why the next president must rebuild, not just restore, the administrative state
COMMENTARY | A reconstructed and reimagined administrative state is crucial to restoring effective government.
- Tom Shoop
Management
That time one agency shut down for one day and changed government forever
COMMENTARY | Forty-five years ago, the government shutdown was born.
- Tom Shoop
Management
For DOGE, it was all in the name
COMMENTARY | Elon Musk made a mockery of government reform.
- Tom Shoop
Management
That time when calling a president ‘old’ was a compliment
You’ve probably heard of Old Hickory. But what about Old Public Functionary?
- Tom Shoop
Management
In Defense of Bureaucracy
COMMENTARY | The administrative state is where things get done.
- Tom Shoop
Workforce
Trump’s plan to slash the federal workforce isn’t the first, it’s just the worst
COMMENTARY | The triple-meat-cleaver approach to workforce “reform.”
- Tom Shoop
Breaking News
Management
Jimmy Carter, architect of the last major civil service reform, dies at 100
During his one-term presidency, Carter devoted considerable attention to federal management.
- Tom Shoop
Management
Good luck, Department of Government Efficiency
COMMENTARY | It sounds like a federal agency, but its job is to get rid of them.
- Tom Shoop
Management
What happens to government when a president bows out
An incumbent’s decision not to seek reelection complicates more than the electoral process.
- Tom Shoop
Management
The continuing irresolution to fund the federal government
COMMENTARY | Congress just keeps getting worse at passing spending bills. There are consequences.
- Tom Shoop
Management
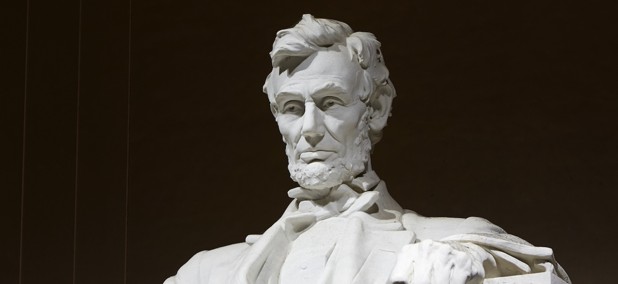
That Time Abraham Lincoln went to a war zone to escape office-seekers
The front lines of the Civil War were a vacation compared to being literally stalked in Washington.
- Tom Shoop
News
Saying goodbye to a giant in government journalism: Charlie Clark, 1953-2023
Clark, a former senior correspondent for GovExec, died Wednesday after a brief illness.
- Tom Shoop
Oversight
What I learned covering government for 34 years
The privilege of reporting on the stuff that really matters.
- Tom Shoop
Workforce
6 places where federal employees actually work in swamps
A tour of government-owned wetlands.
- Tom Shoop
Management
That time the vast majority of federal employees worked outside Washington
That time is now.
- Tom Shoop
Workforce
Tom Hanks thinks he would be the best ever at this federal job
The actor’s ideal career would involve working for Uncle Sam.
- Tom Shoop
Management
That Time acronymic management fads were all the rage
When an alphabet soup of concepts for organizational improvement swept through government.
- Tom Shoop
Workforce
Meet the long-shot presidential candidate who wants term limits for federal employees
Vivek Ramaswamy also pledges to eliminate unions, move workers out of Washington and end “pro-lazy” remote work.
- Tom Shoop
Workforce
Trump: I’ll Make Feds Pass Test on Constitution to Keep Their Jobs
Former president previously said the document was “like a foreign language.”
- Tom Shoop
Management
That Time the Federal Retirement Wave Never Happened
Almost 25 years after the first dire warnings, we’re still waiting on the tsunami.
- Tom Shoop