Author Archive
Megan Garber
Management
Good Riddance to the Handshake
A terrible custom is gone for good. Hallelujah.
- Megan Garber, The Atlantic
Oversight
An Indelible Image From Trump's 'On Both Sides' Press Conference
Once again, the chief executive chose his own words over the ones that had been prepared for him.
- Megan Garber
Oversight
‘Covfefe’: A Typo? A Conspiracy? A Metaphor for America?
According to Sean Spicer, President Trump's garbled late-night tweet was something much more than it seemed.
- Megan Garber, The Atlantic
Management
Are We Having Too Much Fun?
In 1985, Neil Postman observed an America imprisoned by its own need for amusement. He was, it turns out, extremely prescient.
- Megan Garber, The Atlantic
Management
'I’m Moving You to BCC'
Etiquette experts on the small mercies we can grant each other over email
- Megan Garber, The Atlantic
Oversight
Hillary Clinton, Tracy Flick, and the Reclaiming of Female Ambition
The woman president has long been a feature of American pop culture. The woman candidate, though, is rarer—and even more fraught.
- Megan Garber, The Atlantic
Management
Casual Friday and the ‘End of the Office Dress Code’
The day—a celebration of conformity disguised as a celebration of individuality—helped to bring about the current dominance of “business casual.”
- Megan Garber, The Atlantic
Management
Here's Why Carly Fiorina Was the Consensus Debate Winner
The only female candidate on the GOP debate stage proved she could hang with the boys—but also represent “women all over this country.”
- Megan Garber, The Atlantic
Management
The (Real) Story of the White House and the Big Block of Cheese
American democracy's most famous dairy product, fact-checked.
- Megan Garber, The Atlantic
Tech
A Little Ship Just Saved the International Space Station
Meet the Georges Lemaître, which helped the orbiting laboratory—currently home to six humans—to avoid a potentially disastrous collision with space junk.
- Megan Garber, The Atlantic
Management
Wait, Why Another 'Czar'?
To fight Ebola, President Obama has appointed the U.S.'s latest ... Russian emperor? Here's a brief history of a strange title.
- Megan Garber, The Atlantic
Management
Why Presidents Are Also Celebrities
The Roosevelts transformed the United States—and made its leaders into stars.
- Megan Garber, The Atlantic
Management
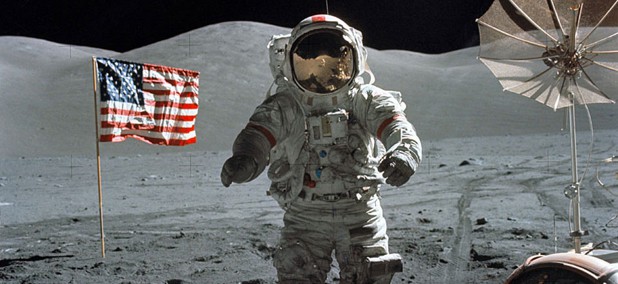
How Do We Welcome Astronauts Back to Earth? By Making Them Go Through Customs
Triumphant returns are also a triumph for bureaucracy.
- Megan Garber, The Atlantic
Tech
Irradiated Turkey, Thermostabilized Yams: Thanksgiving Dinner in Space
If you're celebrating the holiday outside of Earth, you'll enjoy a bird that "resembles sliced deli meat" and stuffing that has "a broth-heavy, institutional flavor."
- Megan Garber, The Atlantic
Management
Space Is Now a Reality TV Show
Chris Hadfield's return from the International Space Station marks a new era for the final frontier.
- Megan Garber, The Atlantic
Management
Would You Take a One Way Ticket to Mars?
Mars One is not the first project hoping to permanently go where no man has gone before.
- Megan Garber, The Atlantic
Management
Meteorite Strikes Are Actually Quite Common
Earth gets hit up to 10 times a year, experts say.
- Megan Garber, The Atlantic
Management
What Does the Sun Sound Like?
A NASA fellow searches for sounds lost in the vacuum.
- Megan Garber, The Atlantic
Management
Hillary Clinton traveled 956,733 miles during her time as Secretary of State
During her tenure, Clinton also visited 112 countries.
- Megan Garber, The Atlantic
Defense
Women in combat: An idea whose time has come, aided by technology
Many of the arguments against "bands of sisters" are moot. In part because of improved tools.
- Megan Garber, The Atlantic