Author Archive
Connor Simpson
Defense
Obama Requests $500 Million for 'Moderate' Syrian Rebels
Any potential recipient would be properly vetted first, the administration promised.
- Connor Simpson, The Wire
Management
FBI Director: Don't Let Weed Stop You from Applying to the FBI
Increasingly outdated anti-marijuana policy is complicating the bureau's efforts to fight cyber crime.
- Connor Simpson, The Wire
Defense
The Psychologist Behind the CIA's Torture Program Desperately Wants to Speak Out
Non-disclosure agreements with the government are holding him back.
- Connor Simpson, The Wire
Oversight
Obamacare Enrollment Results Will Come Down to the Wire
The latest numbers indicate the health care law could sign up 7 million people by the March deadline.
- Connor Simpson, The Wire
Management
Canada's Government Basically Never Closes for Snowstorms
Part of the reason is each department makes its own decision on a case-by-case basis.
- Connor Simpson, The Wire
Defense
Report: Russian Diplomats Who Scammed Medicaid Were Also Spying on the U.S.
It's unclear how many were spies.
- Connor Simpson, The Wire
Defense
New Deal Could Keep U.S. Troops in Afghanistan for 10 More Years
If signed by both countries, U.S. military operations in Afghanistan could continue until 2024.
- Connor Simpson, The Wire
Management
Tim Geithner Finally Moving to Wall Street
Former Treasury secretary hasn't worked in the private sector in more than 25 years.
- Connor Simpson, The Wire
Management
Navy Officials Accused of Taking Cash, Hookers and Lady Gaga Tickets
Gifts allegedly came in exchange for information that led to contractor overcharging.
- Connor Simpson, The Wire
Defense
FBI Releases Chilling Security Camera Footage of Navy Yard Shooter
Video is part of a full report on what the bureau knows about Aaron Alexis so far.
- Connor Simpson, The Wire
Defense
The Justice Department's AP Leaker Was an Ex-FBI Agent
Sachtleben will plead guilty to charges of unlawfully disclosing national defense information and face 43 months in prison.
- Connor Simpson, The Wire
Management
What It's Like to Work for a Background Check Contractor
Former USIS workers say they faced pressure to churn out clearances quickly.
- Connor Simpson, The Wire
Oversight
Hillary Clinton's Not in a Hurry to Run for President
Former secretary of State admits the Oval Office is on her mind.
- Connor Simpson, The Wire
Management
Report Says Budget Cuts Led to Security Lapses at Navy Yard
Convicted felons received unauthorized installation access, audit finds.
- Connor Simpson, The Wire
Defense
What We Know About the Navy Yard Victims
Shooting left 13 dead, including the gunman.
- Connor Simpson, The Wire
Defense
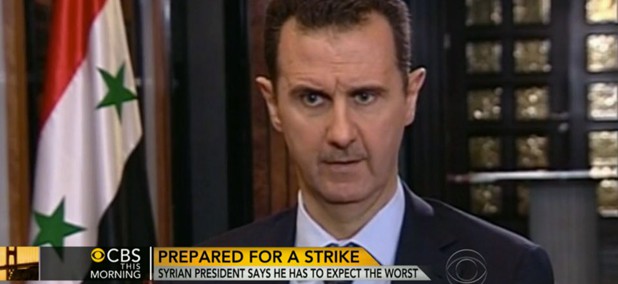
Assad Presents His Defense Against the U.S.
Syrian president claims there is no evidence tying him to Aug. 21 chemical attacks.
- Connor Simpson, The Wire
Defense
The State Department Will Send Someone to North Korea to Rescue Kenneth Bae
Bob Kind, the special envy for North Korean human rights issues will make the trip on Friday.
- Connor Simpson and Abby Ohlheiser, The Wire
Oversight
NSA Bugs United Nations With Enthusiasm, Documents Suggest
The agency also has bugs in 80 embassies and consulates around the world, Der Spiegel reports.
- Connor Simpson, The Wire
Defense
The Internet Made the Military Stop Selling Playboy
Magazines will be pulled because nobody is buying them, not because of the content.
- Connor Simpson, The Wire
Management
Jack Lew: No Debt Limit Fight This Fall
'Congress can't let us default,' Treasury secretary says.
- Connor Simpson, The Wire