Back in the Saddle
Therapy programs pair horses and healing for wounded veterans.
Air Force veteran Alicia Watkins lost everything after she returned from tours of duty in Afghanistan and Iraq and isolated herself from friends and family. She was homeless and living in her car when she accepted an invitation to Join-Up, an intensive three-day program in Solvang, Calif., that pairs abused and neglected horses with self-isolated veterans with post-traumatic stress disorder.
“Horses are flight animals,” Monty Roberts, creator of Join-Up, told the American Forces Press Service. “If they don’t trust it, they need to get away from it. That’s how a veteran feels, too.”
Training horses often involves using violence to force them into submission. Roberts prefers a nonviolent training style he calls “gentling” or “natural horsemanship.” The program is based on trust. “The horses we see that were traumatized and abused never forget it,” he says. “But you can mask it over with good behavior, and that’s the same
with veterans.”
Watkins found relief among the Join-Up participants—both the horses and the other veterans—who understood her suffering and shared her desire to heal.
More than 30 Veterans Affairs Department medical centers also provide equine-assisted therapy to wounded warriors. These six- to 12-week programs match vets who have identified specific goals with trained therapy horses. Veterans begin with grooming their horse and nurturing communication skills then riding on trails. The veteran and the horse gradually become a herd of two.
- Jean Fogarty
Upward Mobility
Created in 1978, the Senior Executive Service was envisioned as a mobile corps that would bring excellence across agencies, a study by the Partnership for Public Service and McKinsey & Co. noted, but nearly half its members have never changed jobs.
Trip Tips
With the recent uproar over what feds are up to on business trips, it might be time to review the Federal Travel Regulation, most recently updated in December 2011.
The only people authorized for temporary duty travel allowances are government employees, interviewees and family members who are “temporarily located to safeguard their lives.” So think twice before inviting your spouse along to Las Vegas on the taxpayers’ dime.
Guidelines instruct agencies to “identify opportunities to reduce costs in selecting a particular conference location and facility.” Try to identify those opportunities prior to your eighth preplanning trip.
Employees are prohibited from using a government-issued charge card for personal reasons while on official travel. If you’re looking for a little local nightlife, you’ll have to pay for it yourself.
Yes, hungry feds, “light refreshments” are allowed. Examples in the guidelines include: cookies, pretzels and soft drinks, not artisan cheese trays or $4 shrimp.
Penalties for defrauding the government can include a fine of up to $10,000 and imprisonment up to five years. This might seem self-explanatory, but you’d be
surprised.
- Andrew Lapin
Tech Savvy Response
Thad Allen shares lessons learned after the BP oil spill.
Two years after an oil rig explosion roiled the Gulf of Mexico, Government Executive caught up with retired U.S. Coast Guard commandant Adm. Thad Allen, who led the federal response. Now at Booz Allen Hamilton, he shared his perspective on social networking’s role during crises.
How he used new media to help after the BP well blowout:
Rather than let false rumors of containment or contamination go viral, Allen propped up a website that streamed BP’s live video from the scene to counter misinformation. A joint information center tracked Tweets and other social media around-the-clock. It is less painful to be transparent from the outset than to disclose information later, he adds. “You can suffer, you can try to adapt or you can try to manage what’s going on,” Allen says.
How data analysis has changed since he graduated from the U.S. Coast Guard Academy in 1971:
Information sharing has moved light years beyond the radio teletype that Allen used in the early 1970s. Even in 1977, “every workstation had four computers” at the El Paso Intelligence Center in Texas, where he was assigned to drug smuggling cases. But the setup engendered trust, Allen notes. “Trust is an automatic byproduct of just trying to get together and get the job done.”
Next, government should try customizable home pages to exchange real-time intelligence, he says. Legislation now requires the Pentagon to make public the coding for the National Security Agency’s Ozone Widget Framework, a tool similar to iGoogle. The framework creates a Web portal that aggregates analytical tools pertinent to a mission, in the way that the Google app displays live news feeds and other updates. “If they can do it in the military, it begs the question of why can’t they do this in places like the Southwest border.
- Aliya Sternstein
Virtual Visionaries
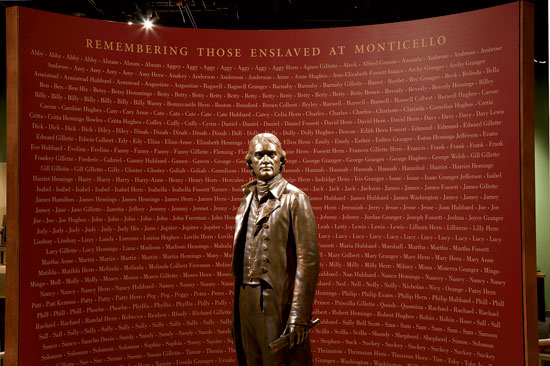
Imagine being able to view the Smithsonian Institution’s trove of more than 100 million artifacts without stepping foot in its 19 museums. Techies in the Smithsonian’s Digitization Program Office are using a newfangled scanner and printer to create 3-D printed replicas, like this Thomas Jefferson look-alike, for display online or off-site. Still a fledgling effort,the program has a long way to go. But it’s literally history in the making.
NEXT STORY: Food Safety On the Line






