Government Executive August 1998 Vol.30, No.8
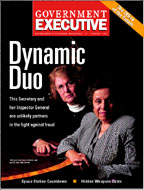 Dynamic Duo
Dynamic Duo
The Secret's Out
The National Security Agency is losing ground in the fight to keep hard-to-find cryptography experts from being lured to greener pastures.
Price Check
It's not just the eye-popping cost of new weapons that is squeezing the Defense Department, but the cost of operating, maintaining and then disposing of them.
Out of Orbit
Beset by cost and schedule overruns and beleaguered by congressional criticism, NASA is struggling to complete its biggest and most complicated program ever, the International Space Station.
Cracking the Whip
An abrasive newcomer charged with leading a crucial management survey has alienated the agency's managers. How can his supervisor get the project back on track?
Special Section: Office Products Guide
The new office of the National Partnership for Reinventing Government offers a glimpse of the office of the future. Also, the latest trends in furniture, faxes, dictation equipment and more.
Departments
Editor's Notebook
Managing Technology: Intranets Extend Their Reach, Time for a Desktop Upgrade?
Marketplace: Drawing the Line on Outsourcing, Let Contractors Take the Risks
Thinking Ahead: Former Federal Reserve Chairman Paul Volcker
Travel: Business Can Be a Real Trip
NEXT STORY: Eighteen Months and Counting






