
The defense industry is chock full of acronyms, describing everything from specific agencies to new technologies and mission-critical operations. Recently, another acronym has entered the conversation: CMMC.
The Cybersecurity Maturity Model Certification was first introduced in early 2020, when the Office of the Under Secretary of Defense for Acquisition & Sustainment published CMMC as a verification system requiring vendors to engage a third-party to assess their internal cybersecurity practices and process maturity. CMMC comes on the scene as the Defense Department seeks to combat increased threats from nation-state adversaries in addition to standard cybersecurity risks like phishing or social engineering. But for many agencies, ensuring system security is easier said than done. After all, the Defense Department employs hundreds of thousands of contractors and sub-contractors — all of whom present varying degrees of security risk. CMMC requires agencies to vet and review the companies they choose to partner with, ensuring they have the necessary security infrastructure built into their products and services.
While the CMMC guidance was released in January 2020, there are still a number of questions about what exactly it means for agencies and contractors alike.
“One misconception that I hear a lot is that CMMC is a checkbox, it’s a one-time thing,” says Cameron Chehreh, chief technology officer and vice president for Dell Technologies Federal Systems. “People think, ‘I'm going to get to a certain level. I'm going to check that box, I'll set it aside and I'll come back to it next year.’ And that's really a misnomer.”
Instead, Chehreh says that CMMC is intended to fundamentally change an organization and empower people to take an active role in defending their agency from cyberthreats.
“It's an ongoing process that helps you operate in a more secure manner. It’s a journey rather than a destination,” he says.

“One misconception that I hear a lot is that CMMC is a checkbox, it’s a one-time thing. People think, ‘I'm going to get to a certain level. I'm going to check that box, I'll set it aside and I'll come back to it next year.’ And that's really a misnomer.”
CAMERON CHEHREH | chief technology officer and vice president, Dell Technologies Federal Systems

Understanding the Defense Industrial Base
Chehreh has spent over two decades building products and solutions that help federal civilian and defense agencies protect against cyber threats and attacks. He began his career as the fifth employee at a small Annapolis-based application services startup called USInternetWorking Inc. One night, the company’s CEO and founder gave Chehreh and his colleagues two-hundred dollars to go out to a bar and come up with a tagline for the company. After several hours, the group of employees finally landed on one: Software as a Service. It was on that fateful night that Chehreh’s passion for digital transformation and cybersecurity truly blossomed.
Throughout his extensive career in the federal IT space, Chehreh has noticed that people fall into two camps when it comes to solving the nation’s most pressing security challenges.
“Some people look at these threats and get extraordinarily scared and can't deal with the information presented to them. Others take solace in the fact that they’re contributing in whatever way possible to protect the country and its people,” he explains.
Chehreh finds himself in the second camp. For organizations working toward CMMC certification, he recommends a similar approach: Understand your role in the process. “Many private sector organizations might not actually know that they need to participate because they are under the impression that they don’t provide products or services to the government,” he says.
Chehreh offers up the example of a fastener business that produces nuts, bolts, screws and nails.
“This type of business may not supply directly to the government, but they might be selling to a Northrop Grumman or a General Dynamics, because — let's face it — it takes a lot of fasteners to build a plane, a ship, a tank and all of those other products that ultimately become consumed by the government.”
Of course, nuts and bolts may not seem like risky business. But Chehreh says that without the proper security measures in place, these fastener businesses could pose grave national security risks.
“If an adversary knows how many nuts and bolts it takes to build a tank, they know the tensile strength of the steel of a bolt and they know how the tank is designed, they now know how to build ammunition or a bomb to drop on the tank,” he explained.
For Chehreh, one of the most fascinating aspects of cybersecurity is that often, “it’s not always the sophisticated things that get us; sometimes, it’s the basics.”
Many private sector companies are involved in government activities, if indirectly, so Chehreh recommends organizations look beyond their own business activities and investigate how their customers are using these products and services. Determining this customer base — and who these customers are selling to — will help private sector companies better understand whether or not they need to participate in CMMC.

“Some people look at these threats and get extraordinarily scared and can't deal with the information presented to them. Others take solace in the fact that they’re contributing in whatever way possible to protect the country and its people.”
CAMERON CHEHREH
Overcoming the Starting Hurdle
Of course, for many organizations, beginning the CMMC journey is the hardest part.
“A lot of people find it overwhelming, and many don’t know where to begin,” Chehreh says. “But my advice is this: start the same way you start everything. Ask yourself: ‘Do I truly understand my current profile? Do I understand my current baseline?’”
Once organizations take that first step, the rest will fall into place.
“That’s when the natural curiosity of a human being kicks in, you ask the simple question of, ‘How secure am I today?’” Chehreh explains. “And, ‘What measures do I have and what data do I have that demonstrates my ability to answer that question?’”
Chehreh applauds the federal government for creating and implementing the CMMC framework. He says it’s the first of its kind to offer a clear definition of cyber hygiene for organizations to measure themselves against.
Do I truly understand
my current profile?

How am I secure today?
What data do I have to
answer that question?
For the longest time, when we talked about cyber, it was very ethereal,” says Chehreh. “People didn't know how to put their finger on what specifically they needed to do to create a common baseline of knowing they’re taking the appropriate preventative measures to be safe.”
CMMC also provides defense agencies and contractors with a tangible way to measure their cyber hygiene.
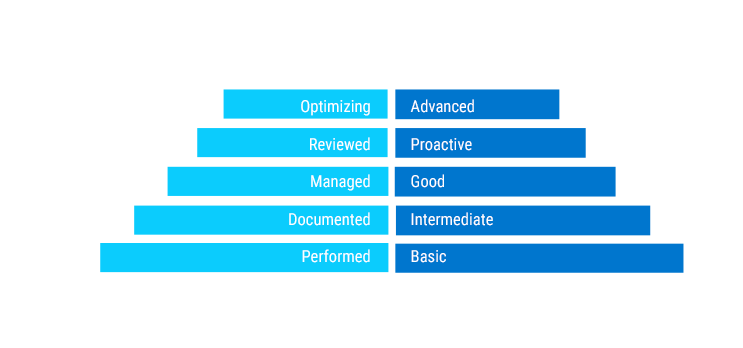
“You can't manage what you can't measure,” Chehreh says. “And what CMMC does is it gives us an opportunity to measure cybersecurity progress through maturity levels.”
As organizations look to improve their cybersecurity posture, there are several new solutions on the market to help vendors manage the CMMC process more effectively. But even Chehreh — perhaps one of the biggest champions of federal cloud adoption and IT transformation — says successfully securing government systems will depend on more than technology alone.
“It's always about people, process and technology,” he says. “It can't be one or the other. It has to be a summation of all three in order to achieve the CMMC certification.”

PEOPLE
PROCESS
TECHNOLOGY
Learn more about how Dell Technologies’ suite of security products and services can help your agency begin the journey toward CMMC certification.
